By Nathan Fain
Incomplete: must create detailed diagram for compression functions.
The following simplifies the specification of SHA-1 in an easy to digest form. First we will cover the general structure of the algorithm. Detail of the expansion and compression routines are covered separately.
 First we start with a message. The message is padded and the length of the message is added to the end. It is then split into blocks of 512 bits (Figure 2).
First we start with a message. The message is padded and the length of the message is added to the end. It is then split into blocks of 512 bits (Figure 2).
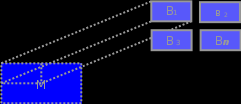
(Figure 2)
The blocks are then processed one at a time. Each block must be expanded and compressed. The value after each compression is added to a 160bit buffer called the current hash state. After the last block is processed the current hash state is returned as the final hash. A overview of this procedure can be seen in Figure 3.

(Figure 3)
Let’s look more closely at the expansion and compression functions. For expansion each 512 bit message block is separated into chunks of 32 bits. As you can see in Figure 4 these 16 chunks are then used to create 64 more chunks for a total of 80. Details of how this is done are described later.

(Figure 4)
Now all 80 of these chunks are compressed into a 160 bit value which is added to the current hash state (Figure 5):
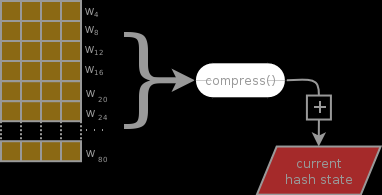
(Figure 5)
Figure 5 shows one block being processed. The expansion and compression functions are repeated for each block with the return constantly being added to the current hash state buffer.  Once all blocks have been processed it is this value that is returned as the hash of the message.
Once all blocks have been processed it is this value that is returned as the hash of the message.
3 tasks were generalized above: How the message is prepared before processing, how exactly the block is expanded to 80 chunks (Figure 4) and how those chunks are compressed (Figure 5). It is not essential to understand them in detail but should you desire, here are the details.
Message Preparation
The message is prepared in 4 steps:
- Append a single binary 1 bit to the message
- Split into blocks of 512 bits each (Figure 2 above)
- The last block must be equal to 448 so that we can append the message length (next step). If it is under pad with binary 0 bits until equal to 448. If over, pad until it is 512 bits and create an additional block of 448 binary 0 bits.
- Append the length of the original message to the last block. Represent this length as a 64 bit integer (making the last block equal to 512 bits).
I should also mention that before we process any blocks we must initiate the hash state buffer. The buffer is actually 5 separate 32 bit integers:
- h0 = 67452301
- h1 = EFCDAB89
- h2 = 98BADCFE
- h3 = 10325476
- h4 = C3D2E1F0
Block expansion
 Each 512 bit block is split further into 32 bit chunks (“words“) as seen in Figure 4. These 16 chunks are then expanded to a total of 80. The processes of expansion is a simple XOR of 4 values. For instance, the next chunk, chunk 17, is created by XOR’ing together chunk 17-3, 17-8, 17-14 and 17-16. For chunk 18 run the same processes but subtracting from 18 instead of 17. This continues until all 80 have been created. This can clearly be seen in the animation to the right. (If the animation is not playing reload the page.)
Each 512 bit block is split further into 32 bit chunks (“words“) as seen in Figure 4. These 16 chunks are then expanded to a total of 80. The processes of expansion is a simple XOR of 4 values. For instance, the next chunk, chunk 17, is created by XOR’ing together chunk 17-3, 17-8, 17-14 and 17-16. For chunk 18 run the same processes but subtracting from 18 instead of 17. This continues until all 80 have been created. This can clearly be seen in the animation to the right. (If the animation is not playing reload the page.)
Block compression
 This work is licensed under a Creative Commons Public Domain License and may be used however you wish. For sources to Dia based diagrams, contact me.
This work is licensed under a Creative Commons Public Domain License and may be used however you wish. For sources to Dia based diagrams, contact me.
Leave a comment